Introduction to TLS, jks and keystores

Let’s face it: certifiates, key management, ssl/tls has never been any fun for any Java developer. That’s why I was also avoided this topic for as long as possible. And the time came to finally gather all I know , or rather: what I don’t know, just for reference.
Introduction
Purpose of the blog post
My purpose here is to present an overview of the whole area of certificates, certifiate authorities, keys, key management (especially around proprietary Java file format) and tooling. It is better to have a bit of wider context, to build a map of understanding and zooming into specific areas when one needs it than to be too shallow or too deep.
Of course, my preferred depth is different than yours, so you may feel this blog entry is overwhelming (or superficial). It is OK, we all learn and are just on different levels of understanding. If you want, you can follow along; if it is too confusing, go ahead and try to find better references. These topics are covered widely online. I’m not trying to teach (although you are welcome to learn) but I’m rather trying to order the information I have and to give them sonme structure and context.
Brief overview of SSL/TLS encryption
SSL/TLS (Secure Sockets Layer/Transport Layer Security) primarily operates on the Transport Layer of the OSI (Open Systems Interconnection) model. In the OSI model, this is Layer 4, commonly referred to as the “Transport Layer.”
SSL/TLS is responsible for securing the communication between two devices, typically a client and a server.
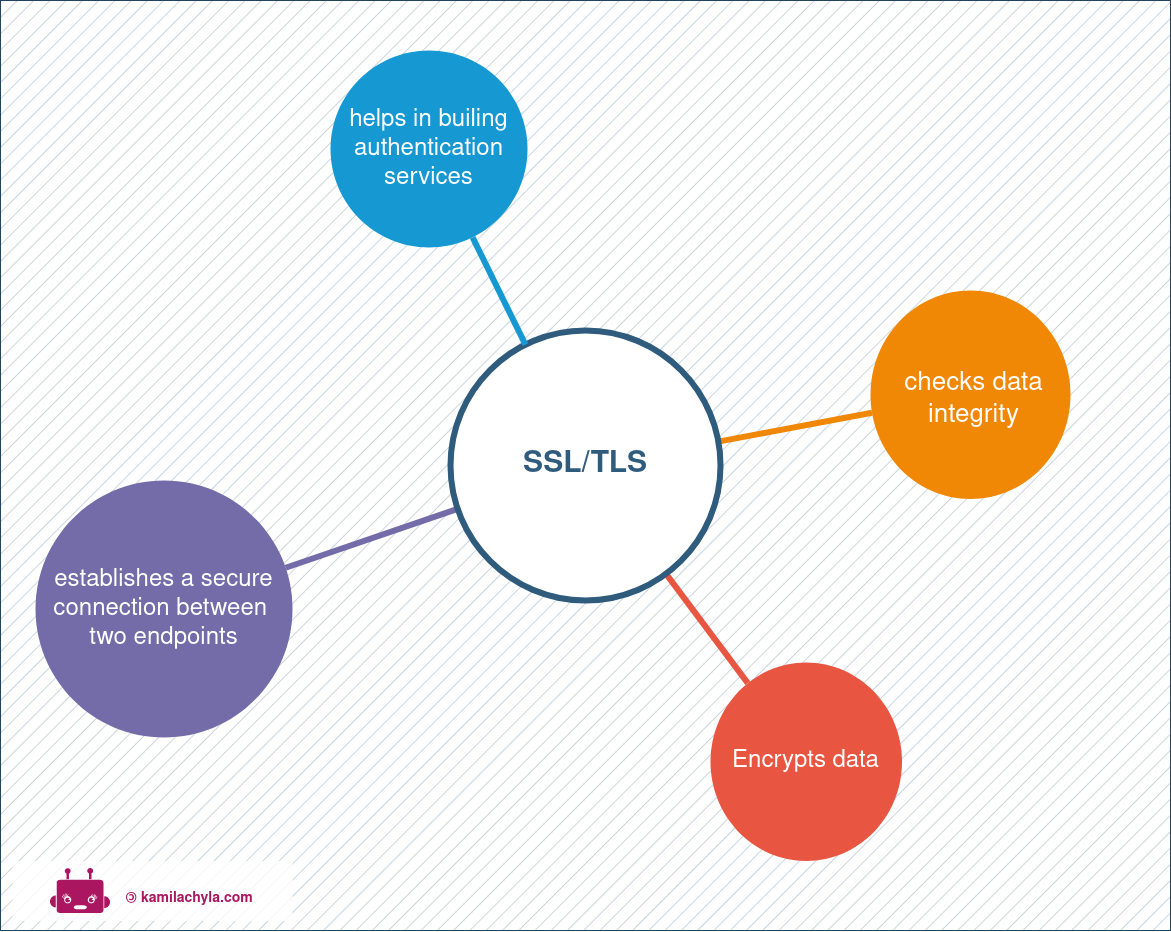
It does this all before passing it up to the higher layers for further processing.
Importance of SSL certificates
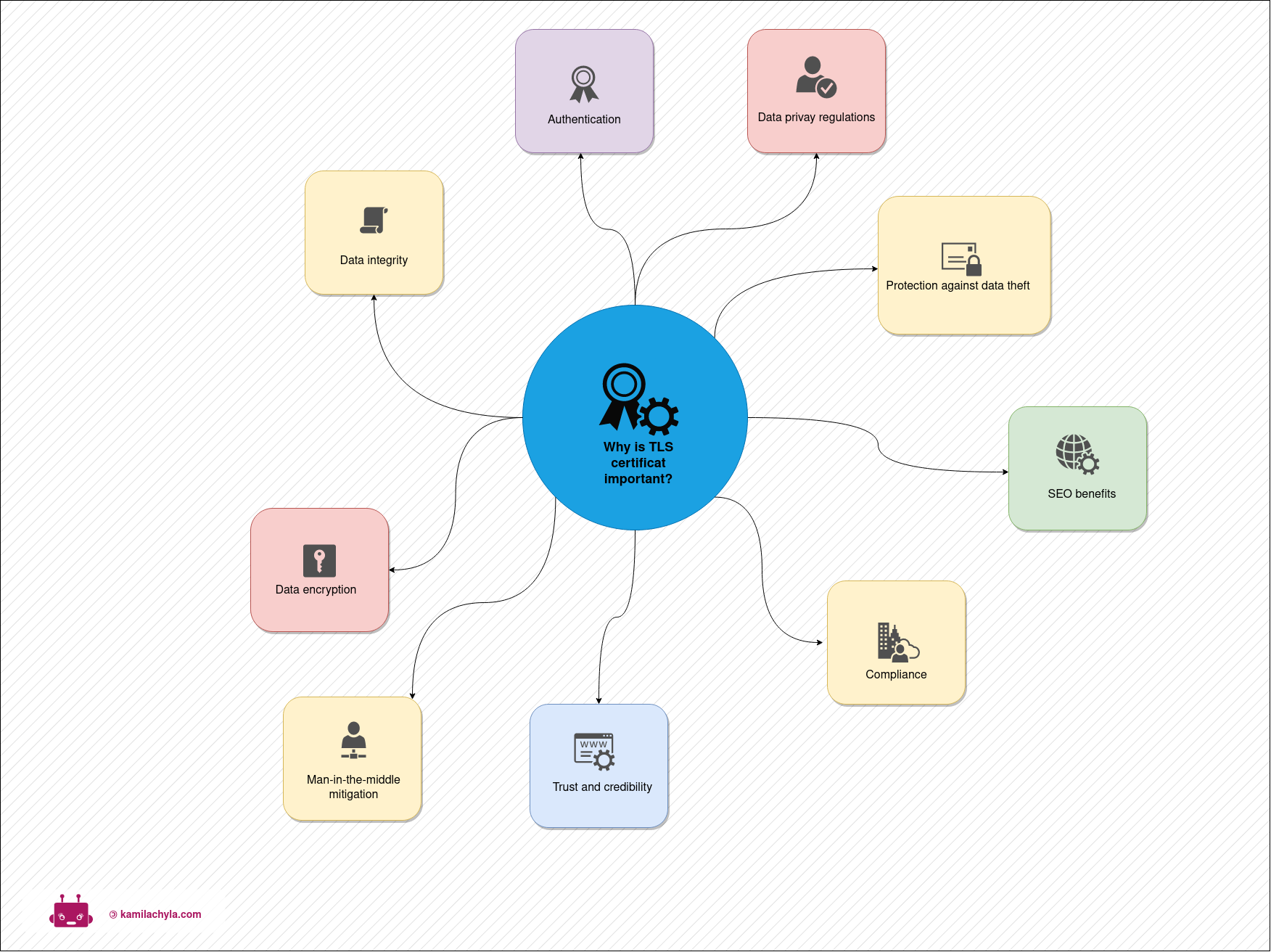
Why do we care about TLS? We know the basic (and correct) answer which is security. Let’s be a bit more precise and list more specific reasons:
| Short Reason | Explanation |
|---|---|
| Data Encryption | SSL/TLS certificates encrypt data in transit, ensuring its confidentiality and security. SSL certificates employ cryptographic algorithms to encrypt the data exchanged between a web server and a client’s browser or application. This encryption ensures that the data is secure and cannot be easily intercepted or read by malicious actors. |
| Data Integrity | SSL/TLS certificates verify the integrity of data, preventing tampering during transmission. SSL certificates also verify the integrity of data during transmission. They use hash functions to create unique fingerprints (checksums) of the data, allowing the recipient to confirm that the data has not been altered or tampered with during transit. |
| Authentication | SSL/TLS certificates establish the authenticity of websites, protecting users from impersonation. SSL certificates serve to authenticate the identity of the web server to the client. When a client connects to a website secured with SSL, the certificate provides assurance that the website is indeed operated by the entity it claims to be. This helps prevent phishing and man-in-the-middle attacks. |
| Trust and Credibility | SSL/TLS certificates build trust by displaying security indicators, enhancing user confidence. SL certificates are issued and signed by trusted Certificate Authorities (CAs), organizations that verify the authenticity of websites and issue certificates to those that meet their security standards. As a result, SSL certificates are trusted by web browsers and devices, and they play a crucial role in building trust with users. |
| Compliance | SSL/TLS certificates are mandated by regulations to safeguard sensitive data and privacy. |
| SEO Benefits | Websites with SSL/TLS certificates improve search engine rankings, increasing visibility. Search engines like Google give preference to websites with SSL certificates in search rankings, which can lead to increased visibility and improved search engine optimization (SEO). |
| Protection Against Data Theft | SSL/TLS safeguards sensitive information like login credentials and financial data. |
| E-commerce Security | SSL/TLS ensures secure transactions, boosting customer trust and online business success. |
| Data Privacy Regulations | SSL/TLS helps meet legal requirements for data protection and privacy outlined by regulations. |
| Mitigation of Man-in-the-Middle Attacks | SSL/TLS encryption makes it difficult for attackers to intercept or tamper with transmitted data. |
Understanding SSL Certificates
What is an SSL certificate?
An SSL certificate, which stands for Secure Sockets Layer certificate, is a digital certificate that establishes a secure, encrypted connection between a web server (or other types of servers) and a user’s web browser or application.
Installed on a webserver
If a certificate secures a website, then it prooves that the owner of that website has verified (or prooved) its identity with a trusted third party. This third party is Certificate Authority (CA). Browsers are built such that they trust a group of CAs, so the web browser also trusts the certified website (and displays the padlock icon in the address bar). If you visit such a website and see this icon, you can be assured that your browser really talks to the server it says it talks to, and that the data you send is encrypted and safe.
Browsers are able to switch from HTTP to HTTPS automaticaly and connect to webservers initially using TCP port 80, but then - if the server has SSL certificate installed - using SSL port 443.
The Handshake Protocol
- authenticates the server
- optionally authenticates the client
- negitiate cryptography details
- generate shared secret (key)
The Record Prototol
- isolates each connection
- uses the shared secret to secure communication during session
SSL certificates have also a wider usage, expanding far beyond WWW. Some companies use SSL certs for oher usecases:
- Network Access control (usecase: allow access for wireless devices but protect intranet or corporate portals/resources)
- Virtual Private Network (SSL VPN is based on SSL; allows granular control over application access to web resources)
- Single Sign-On (based on cloud Identiry Providers)
- Internet of Things (digital entity is installed on devide so that oly trusted IoT devices can connect to the network)
Those technologies use SSL underneath as a way to secure communication and/or authenticate users or devices.
Keystore and Truststore
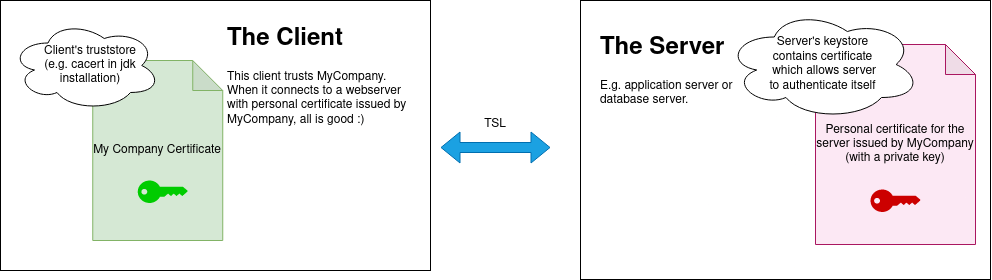
When we talk about keystores and truststores (and soon find out that .jks files can play both roles), it is important to understand what it means.
Keystores and truststores are repositories that contain cryptographic artifacts like certificates and private keys that are used for cryptographic protocols such as TLS.
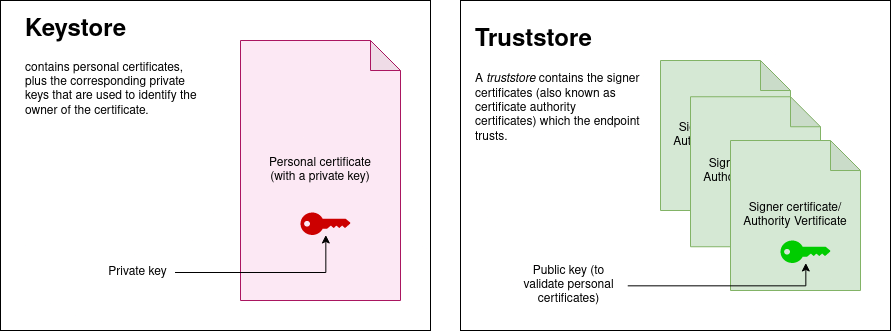
A keystore contains personal certificates, plus the corresponding private keys that are used to identify the owner of the certificate.
For TLS, a personal certificate represents the identity of a TLS endpoint. Both the client (for example, a REST client) and the server (for example, a tcServer, JBoss application server or a database server) might have personal certificates to identify themselves.
- typically it is used by application server to store its private key and site certificate.
- so a keystore.jks file which the application server uses has at least
A truststore contains the signer certificates (also known as certificate authority certificates) which the endpoint trusts. For example, GoDaddy, Verisign, NetworkSolutions and others.
- the truststore is bundled with JDK/JRE in $JAVA_HOME/lib/security/cacerts
- it is used when Java code establishes a connection over SSL.
A signer certificate contains a public key, which is used to validate personal certificates. By installing the server’s signer certificate into the client’s truststore, you are allowing the client to trust the server when it establishes a TLS connection. The same principle is true for a server to trust a client when TLS client authentication is enabled.
JKS files and their role in managing SSL certificates
Java KeyStore (JKS) files play a crucial role in managing SSL certificates, especially within the context of Java applications and servers.
JKS files are a type of keystore, which is a repository for cryptographic keys and digital certificates. Here’s a detailed explanation of JKS files and their role in SSL certificate management:
What Are JKS Files?
According to Wikipedia, JKS is:
(…) a repository of security certificates – either authorization certificates or public key certificates – plus corresponding private keys, used for instance in TLS encryption.
JKS (Java KeyStore) is a proprietary keystore format used in Java applications. It is a binary file,
Role of JKS Files in SSL Certificate Management
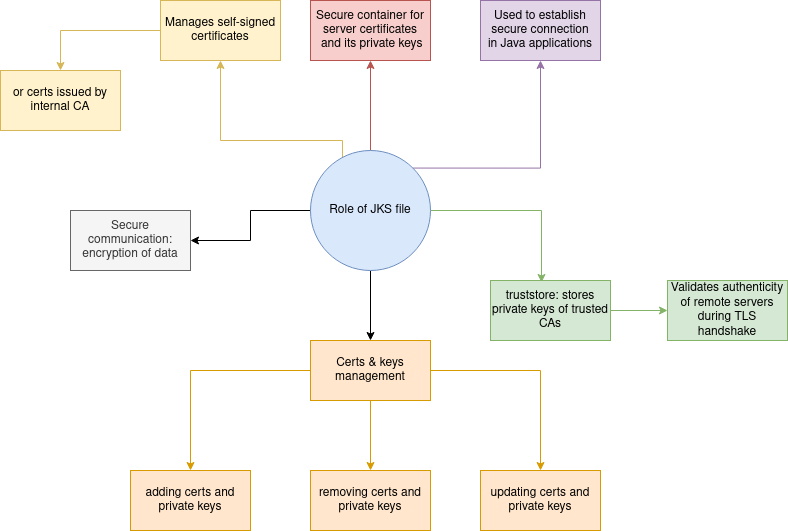
- Storage and Management: JKS files act as a secure storage container for SSL/TLS certificates, including server certificates and their private keys. These certificates are used to establish secure connections in Java applications.
- Truststore: JKS files can also function as truststores, which store the public keys of trusted certificate authorities (CAs). These keys are used to validate the authenticity of remote servers during SSL/TLS handshakes.
- Key Management: JKS files provide a convenient way to manage encryption keys and digital certificates. This includes adding, updating, and removing certificates and private keys.
- Secure Communication: When a Java application needs to establish an SSL/TLS connection (e.g., for HTTPS web communication), it uses the certificates and private keys stored in the JKS file to secure the data transfer.
- Protection of Sensitive Data: JKS files are typically password-protected to ensure the security of private keys and certificates. This adds an additional layer of protection to sensitive cryptographic material.
- Support for Custom Certificates: Organizations can use JKS files to manage their self-signed certificates or certificates issued by their own internal CAs. This is particularly useful in private network environments.
Spring Boot
This is quite a big topic already so I will just throw a link at you. For securing Spring Boot application (in a new way) with SSL, read this blog post. I haven’t tried this API settings yet, it is really worth looking at.
Usage
A great resource for both theory and practical examples is this Medium article.
Note that extracting private keys from .jks file is not supported and you have to install openssl commandline utility to do this.
This script shows how to perform specific operations on keystore files (forked from [Seralahthan][https://gist.github.com/Seralahthan/36b1e38274cc4b18bea27ce928ce2975] ):
Reference
- Medium article Exploring key stores and public certificates
- Wikipedia article about Java KeyStore
- OpenSSH manual
- Keystore Explorer is a GPL-3 free software, a rplacement for keytool and jarsigner
- Types of ssl certificates
- What is ssl?
- Best practices to protect ssl certificates
- Securing Spring Boot Applications With SSL
- Keytool command documentation
- Medium article Java developer guide to SSL